- Cloud Services: optimise hybrid and multi-cloud environments, ensuring scalability and resilience in IT infrastructure. Delve into trends like edge computing, serverless architecture, and the role of cloud-native technologies
- No Code / Low Code: accelerate application development and foster innovation, reducing development costs, and bridging the skills gap in IT teams.
- Open Source: leverage Open Source to drive innovation, collaboration, and cost-efficiency in software development. Fast-track open-source adoption and leverage strategies for managing security and compliance
- Digital Transformation Acceleration: harness the power of artificial intelligence, cloud computing, and other emerging technologies to remain competitive and innovative
- Talent Acquisition and Retention: The persistent shortage of skilled IT professionals continues to challenge CIOs in building and maintaining high-performing teams. What do you need to do to attract top-tier talent, upskill existing employees, and foster a culture of continuous learning to navigate talent scarcity.
- Data Governance and Privacy Compliance: As data volumes explode, learn more about responsible data management, governance, and compliance with evolving data privacy regulations. How can you balance data utilization with ethical considerations and legal requirements?
- Resilient Infrastructure: Discuss the best ways to optimize your IT architecture to enable scalability, agility, and seamless integration while minimising downtime risks
WELCOME TO INFOTECH 2025 Where Visionary CIOs Shape Tomorrow's Digital Landscape
Discover the ultimate gathering ground for trailblazing CIOs and IT leaders at Infotech 2025. As the technology ecosystem continues to evolve at an unprecedented pace, the role of the CIO has become more pivotal than ever before.
In today’s climate, CIOs are not only technology enablers, but strategic partners who must collaborate closely with other C-suite executives to drive business success in a dynamic but challenging digital environment.
Join us for a transformative day of networking, peer-to-peer discussions and thought leadership to help you navigate the complex intersection of technology, strategy, and leadership.
Infotech 2025 is not just a conference; it's a nexus of innovation, collaboration, and forward-thinking insight. Step into an immersive realm where cutting-edge technologies converge with visionary strategies, fostering an environment where challenges become opportunities and ideas become actions.
Uniting under the banner of "Charting Digital Frontiers through Collaboration," we invite you to engage with an exclusive community of thought leaders, industry
Throughout the event, you'll have the chance to explore the most pressing themes shaping the modern CIO landscape.
From combating emerging threats to architecting resilient and scalable infrastructures for tomorrow's demands, Infotech 2025 will equip you with the knowledge, tools, and connections needed to thrive in an era of rapid change.
Your seat at the Infotech 2025 table awaits – let's shape the future together!

SOME OF OUR ATTENDEES...
JUST SOME OF OUR CONFIRMED PARTNERS...
SPEAKERS, WORKSHOP & ROUNDTABLE LEADERS
250
Thought Leaders on Site
30 +
Solutions on Show
57%
of IT leaders have been given extra budget to cope with the post-Covid WFH scenario
71%
of IT leaders prefer physical events to virtual events
42%
of IT leaders identify data security as a top priority
TOPICS TO BE COVERED INCLUDE
Who Should Attend?
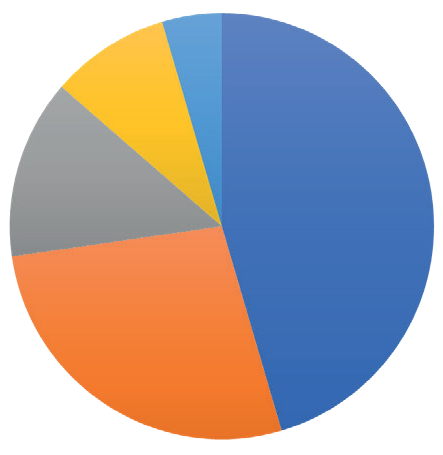
FIELD
IT, 50%
Technology, 20%
Digital, 15%
Data, 10%
Security, 5%
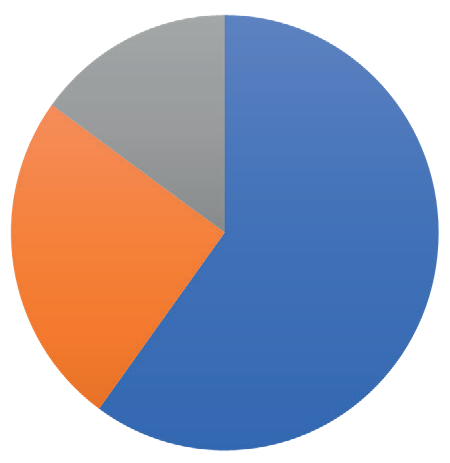
SENIORITY
C-Level, 60%
Directors/VP, 25%
Project Leads, 15%
- WFH & Hybrid
- Digital Transformation
- Cloud
- Collaboration
- Security
- Tooling
- Leadership
“Great discussions with other like-minded experts” – EAO
“A super opportunity to take a step back, reflect, see“A super opportunity to take a step back, reflect, see & learn things from other industries.”& learn things from other industries.” – IQVIA
“The room was truly world class. You could not imagine a better group to discuss what we discussed” – RightCrowd
EPN IT Vision at a Glance / Top 3 reasons you should attend
1: Save time & money by meeting your peers & discovering new technologies all in one place
2: Take part in dynamic discussions, tailored to you and your specific business concerns
3: 10+ hours of networking opportunities. Coordinate meetings, share your experiences, listen to talks.
You have full control of your agenda.
Expert Insights
20 + technology leaders will be delivering data, debate & discussions. Learn from the mistakes & successes of experts from some of the UK’s largest organisations…
Exclusive Features
A new awards show, match-made meetings, a full day of interactive roundtables, complimentary access to co-located events, and much more to take advantage of…
Like-minded Senior Peers
Meet with CIOs, CISO, CDOs, & CTOs to share experiences & get tangible take-home lessons, in both formal & informal networking opportunities…
New Technologies
Join the expo to see the latest technologies that can transform your business. Product demos available to discover what can work for you…
YOUR AGENDA FOR THE DAY (CLICK BELOW TO EXPAND)
8:15 Delegate Registration
09:00 – 09:30 Opening Keynote Presentation: Towards Successful Cyber Attack Remediation
Philip Clayson, CIO and CTO, Jagex
09:30 – 10:00 Keynote Presentation: CISO is not a Swiss Knife: You need to build a balanced team
- The industry seems to be awash with crazy CISO jobs specs; this is no longer acceptable way to search for a CISO
- How can we expect CISOs to handle variety of hands-on responsibilities as well as manage strategy?
- We need to build balanced cyber teams to make sure we can safeguard the business
- How to start with people, processes and only then technology
- Understanding why bad things happen in the first place and how to prevent them
- How to build and implement the right culture
Marius Poskus, Global Vice President of Cyber Security, Global Financial Services
10:00 - 10:45 Solution Spotlight Sessions
This focused session is your opportunity to learn more about the cutting edge technologies transforming the future of the information technology and cybersecurity markets. Each solution spotlight lasts just ten minutes.
10:00 – 10:15 Solution Spotlight: Cyber Resilience Shield: AI powered Ethical Hacking – Sandro Nafzger, CEO, Bug Bounty Switzerland
10:15 – 10:30 Solution Spotlight: Trust no file, Trust no device… a productivity nightmare? – Stefan Liversidge – Solution Engineer, OPSWAT
10:30 – 10:45 Solution Spotlight: From Guardians to Champions: The Evolving Mindset in Data Resilience – Karl Fontanari, Territory Account Manager, ArcServe
10:45 - 11:15 The Threat Landscape - The Current Risks, Measuring Impact to the Business, and Why?
Philip Larbey – Associate Director, Head of VTRAC – EMEA, Verizon
11:15 – 11:30 Coffee Break
11:30 – 12:15 Data Governance and Privacy: Protecting Your Organization's Data
This session will delve into the importance of data governance and privacy, and discuss best practices for protecting your organisation’s data.
- Developing a data governance framework: establishing policies and procedures for managing data throughout its lifecycle
- Ensuring compliance with data privacy regulations: adhering to regulations like GDPR and CCPA
- Implementing data security measures: protecting data from unauthorised access, use, or disclosure
Ranjit Shergill, Data Protection Manager, Phoenix Group
11:30 – 12:15 Less Busy More Impact
- Understand the truth behind our busyness habits
- Practical and behavioural experiments to implement immediately
- Protect yourself and your people from the threat of overworking and burnout
Chris Lovett, Leadership & Simplicity Coach, Author, Speaker
12:30 – 13:15 Protecting your critical assets: how best to spend your money by managing ‘actual’ risks
In today’s rapidly evolving cyber threat landscape, it’s crucial for organisations to understand not just the existence of risks but their actual financial impact. Join us to delve into our innovative approach of Cyber Risk Quantification (CRQ), which provides clear, quantifiable data on the cost of cyber threats, helping you prioritise resources and protect your most critical assets.
Our session will demonstrate how CRQ goes beyond traditional threat profiling by integrating business risk metrics, offering a comprehensive view of your organisation’s vulnerabilities. By marrying business priorities with detailed risk assessments, CRQ offers a clear roadmap for protecting your most critical assets, helping balance cyber expenditures with actual risks.
You’ll gain practical insights to enhance your security posture and make informed decisions that safeguard your infrastructure. Don’t miss the chance to improve your cybersecurity approach and protect your bottom line.
Alistair Neil, Senior Director International Security Sales at Verizon Business
12:30 – 13:15 How is AI impacting the future of email security?
Despite its growing prominence, misconceptions and myths about AI persist, often clouding its true potential and capabilities. Join this session moderated by Robin Mohan, Libraesva Limited Managing Director, to discuss the realities of AI, dispelling common misconceptions, and exchange views on how AI can be effectively harnessed to enhance email security measures.
Robin Mohan, Managing Director, Libraesva
13:15 - 14:15 Lunch
14:15 – 14:45 Keynote: Implementing Business Continuity as part of Corporate Risk Management
Discover how Diabetes UK seamlessly embedded Business Continuity into its Corporate Risk Management framework, overcoming challenges with minimal effort while maximising impact. Learn how aligning BC with organisational objectives and leveraging existing resources can drive resilience and sustainability across your organisation.
- Understanding the critical role of Business Continuity (BC) in managing corporate risk.
- Aligning BC with organisational objectives to ensure resilience and long-term sustainability
- Overview of Diabetes UK’s organizational structure and operational challenges.
- Leveraging existing processes and resources to avoid extensive efforts.
Ali Jaffri, Head of IT Infrastructure and Cybersecurity, Diabetes UK
14:45 - 15:15 Case Study: Our Cybersecurity Journey: From Experiencing a Global Security Incident to Gaining Board Support
Milos Pesic, Chief information Security Officer, Accelleron Industries
15:15 - 16:00 Closing Panel: Strategic Leadership in a Digital World: Navigating Innovation, Security, and Growth
As digital transformation accelerates, CIOs and senior leaders face the complex challenge of balancing technological innovation with robust security measures while driving sustainable growth. This evolving landscape demands a forward-thinking approach to strategy, one that not only leverages emerging technologies but also addresses the risks and opportunities of a hyper-connected world. To remain competitive, organizations must prioritize agility, resilience, and cross-functional collaboration.
- Aligning digital transformation with long-term business objectives, ESG considerations, and market dynamics
- Developing adaptive leadership capabilities to navigate disruption, manage change, and inspire teams in times of volatility
- Attracting and retaining top cybersecurity talent through competitive compensation packages, professional development opportunities and a people-centric work culture
- Developing a robust training and education programme to equip employees with the necessary skills to protect against emerging threats
- Creating a culture where security is a top priority, encouraging employees to report suspicious activity and participate in security awareness training
Ali Jaffri, Head of IT Infrastructure and Cybersecurity, Diabetes UK
Stewart Bertram, Head of Cyber Threat Intelligence, Nomura
Adrian Smith, Chief Information Officer, Adsatis
Philip Clayson, CIO and CTO, Jagex
Alan Pratt, Global Head of Cybersecurity Science and Analytics, HSBC
Moderated by:
Sheetal Thakar, CIO – For Change Management
16:00 End of Conference
YOUR TECHNOLOGY SHOWCASE
Are you looking to showcase what you have on offer? Connect with the leading decision-makers in IT through thought-leadership, brand awareness, & personal 1-on-1 time. Build your trust & demonstrate your value at EPN IT Vision 2025.
Sponsorship packages can be tailored-made to meet your requirements. Contact the sponsorship team to find out how you can utilise your opportunity to meet the CIO community.
- ITSM
- Identity & Access Management
- Communications
- API
- IOT
- Remote IT
- CRM & ERP
- DevOps
- Network Infrastructure
- 3rd Party Risk
- Cloud Management
- Data Management
- AI & Automation
- Mobile & Applications
- Monitoring & Reporting
- Security
TITANIUM
- Exhibition Space in Tier 1 Area
- Product Demo
- Host a Roundtable
- 5 x 121 meetings in the build up and over the course of the day
Co-branding on All Literature - Priority networking
- Bespoke Thought Leadership Dinner the night before
PLATINUM
- Exhibition Space in Tier 1 Area
- Product Demo/ Keynote Speech
- 5 x 121 meetings in the build up and over the course of the day
- Co-branding on All Literature
- Priority networking
- Host a Roundtable
GOLD
- Exhibition Space in Tier 1 Area
- Product Demo
- 5 x 121 Meetings in the build up and over the course of the day
- Co-Branding on All Literature
- Priority Networking
SILVER
- Exhibition space in Tier 2 Area
- 3 x 121 Meetings in the build-up and over the course of the day
- Co-Branding on Some Literature, Networking Sponsorship
BRONZE
- Exhibition space in Tier 3 Area
- Co-Branding on Some Literature
- Networking Sponsorship
ENTRY-LEVEL SPONSORS
- Branded Table in the Coffee Area
- Networking Sponsorship
Take Part in the Conference / Top 3 ways you can gain exposure
1: Meet the decision-makers of corporate technology. Get to know the people who create digital success.
2: Save time & money by touching- base with your existing clients, making new contacts, & showcasing your expertise all in one place.
3: We know the power of face-to-face business networking. You should be part of the conversation.
Thought-Leadership
Position yourself among the leading experts of IT development & application. Let the IT community know that you are integral expert in the conversation.
Brand Visibility
Get your foot in the door as IT leaders seek for new applications & technologies by showing the solution is out there… they just need to know what it is.
Demonstrating Value
Take part in the Product Demonstrations & showcase your capabilities, so that your potential clients can learn that you are right for them