- Sophisticated Cyber Threats and Attacks: As the cyber threat landscape continues to evolve with increasingly sophisticated and persistent attacks, learn how to defend against advanced threats that can bypass traditional security measures
- Supply Chain and Third-Party Risk: Brainstorm the best ways to assess and manage the security posture of vendors, partners, and suppliers to prevent potential vulnerabilities from compromised systems
- Zero Trust Implementation: How can you rethink traditional security models, establish strict access controls, and ensure seamless user experiences?
- Regulatory and Compliance Complexities: Navigate a web of regulations, from GDPR and CCPA to emerging laws, and ensure their organization’s data handling practices align with these requirements
- Talent Acquisition and Retention: The persistent shortage of skilled IT professionals continues to challenge CIOs in building and maintaining high-performing teams. What do you need to do to attract top-tier talent, upskill existing employees, and foster a culture of continuous learning to navigate talent scarcity?
WELCOME TO CYBERSEC 2024 Where Visionary Cybersecurity Leaders Unite to Fortify Tomorrow's Digital Frontier!
Discover the ultimate gathering ground for trailblazing CISOs and cybersecurity leaders at CyberSec 2024. As the technology ecosystem continues to evolve at an unprecedented pace, and every digital interaction carries unprecedented importance, the role of the CISO has never been more critical.
Join us at CyberSec 2024 and discover the insights, strategies, and connections that will empower you to safeguard the digital landscape of the future.
CyberSec 2024 is not just a conference; it's a nexus of innovation, collaboration, and forward-thinking insight.
Our high-level keynote presentations, interactive panels and round table discussions, led by industry luminaries and visionaries, will delve into the most pressing challenges and emerging trends in the cybersecurity landscape.
From AI-powered threat detection to blockchain-driven data integrity, our agenda is tailored to empower you with the tools and knowledge to stay ahead of the cyber curve.
Engage with a community of like-minded professionals who share your passion for defending against digital threats, and explore innovative solutions that will shape the future of cybersecurity.
Your seat at the CyberSec 2024 table awaits – let's shape the future together!
200
Thought Leaders on Site
30 +
Solutions on Show
57%
of IT leaders have been given extra budget to cope with the post-Covid WFH scenario
71%
of IT leaders prefer physical events to virtual events
42%
of IT leaders identify data security as a top priority
TOPICS TO BE COVERED INCLUDE
Who Should Attend?
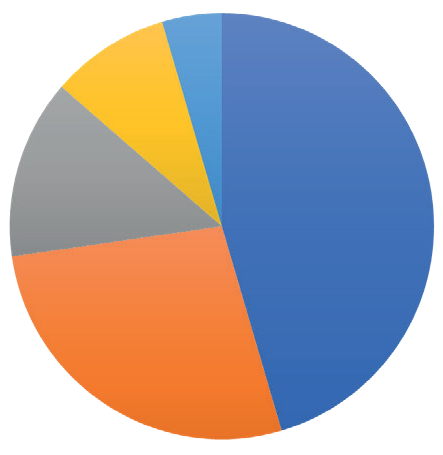
FIELD
IT Security, 50%
IT, 20%
Technology, 15%
Data, 10%
Governance, 5%
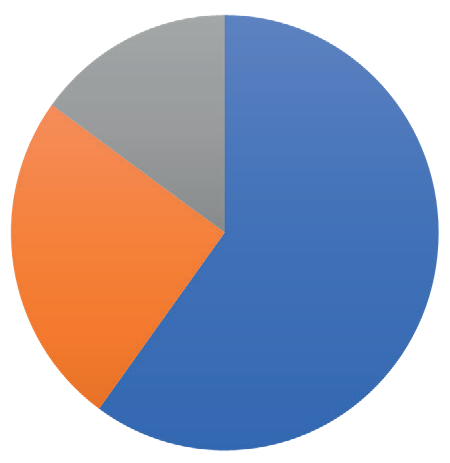
SENIORITY
C-Level, 60%
Directors/VP, 25%
Project Leads, 15%
- WFH & Hybrid
- Digital Transformation
- Cloud
- Collaboration
- Security
- Tooling
- Leadership
“Great discussions with other like-minded experts” – EAO
“A super opportunity to take a step back, reflect, see“A super opportunity to take a step back, reflect, see & learn things from other industries.”& learn things from other industries.” – IQVIA
“The room was truly world class. You could not imagine a better group to discuss what we discussed” – RightCrowd
EPN IT Vision at a Glance / Top 3 reasons you should attend
1: Save time & money by meeting your peers & discovering new technologies all in one place
2: Take part in dynamic discussions, tailored to you and your specific business concerns
3: 10+ hours of networking opportunities. Coordinate meetings, share your experiences, listen to talks.
You have full control of your agenda.
Expert Insights
20 + technology leaders will be delivering data, debate & discussions. Learn from the mistakes & successes of experts from some of the UK’s largest organisations…
Exclusive Features
A new awards show, match-made meetings, a full day of interactive roundtables, complimentary access to co-located events, and much more to take advantage of…
Like-minded Senior Peers
Meet with CIOs, CISO, CDOs, & CTOs to share experiences & get tangible take-home lessons, in both formal & informal networking opportunities…
New Technologies
Join the expo to see the latest technologies that can transform your business. Product demos available to discover what can work for you…
JUST SOME OF OUR CONFIRMED VENDORS...
SPEAKERS, WORKSHOP & ROUNDTABLE LEADERS
YOUR AGENDA FOR THE DAY (Click below to expand)
Registration and Coffee
8:30
Keynote Speech
9:00– 9:30: The Future of Cloud: Microsoft’s Strategy, Key Investments and Future Innovation Areas
- An overview of the core incubations and disruptive technologies shaping the cloud’s future and the next wave of innovation across industry, government and society
- Tomorrow’s cloud structure & capabilities: A 3 – 5-year horizon
- How tech will be prepped for changing standards
- How to gain a foothold today in tomorrow’s key technologies
– Nick McQuire, Director, Product Development, Strategy & Technologies, Microsoft
Solution Spotlight Sessions
9:30 –10:15: This focused session is your opportunity to learn more about the cutting–edge technologies transforming the future of the IT Security market. Each solution spotlight lasts just fifteen minutes.
Spotlight One: Scaling Up from Cyber Security to Cyber Resiliency
- How to make cyber resilience tangible and measurable
- Gain practical tips on how to implement the right policies, processes, and controls
- Why the human layer is one of your most important lines of defense
– Ben Preston, Field Technical Director, Cohesity
Solution Spotlight Two: Zero Trust Security – It’s Not (Just) about Identity – How to Evolve to Meet Today’s Cloud-first, AI-Embracing World
Join Netskope for a practical guide to adapting security to match today’s cloud based infrastructure, AI adoption and hybrid working user – sharing why and how you can move away from traditional security and networking infrastructure to provide better security and performance.
– Paolo Passeri, Senior Director, Head of Product, Personal Workspace Software, Netskope
Spotlight Session Three: Securing Organisations in the AI Era
Stopping the new generation of bad actors, using ML-driven security techniques to gain efficiencies and protecting the approved AI tools
– Yaroslav Rosomakho, VP, Field CTO, Zscaler
Coffee Break
10:15 – 10:45
1-2-1 Meetings/Conference Roundtables/Networking
10:50 – 12:00:
10:50 – 11:20: Best Practices in moving from Cyber Security to Cyber Resiliency
- The impacts of ransomware and wiper attacks seen across the globe demonstrate that our old “wall-and-moat” approach to prevention and detection isn’t working. While at the same time many organisations are struggling build the right operational capability to respond and recover from such a destructive attack in an effective and efficient manner, meaning many simply react rather than respond. Response and recovery from a cyber incident differs from traditional disaster recovery scenarios and in this session we’ll dig deep to understand proven best practices.
- How do we ensure we fully investigate a ransomware attack where much of the evidence is now sat encrypted?
- How can we understand business and regulatory impacts of the data that has been exfiltrated and encrypted?
- What are the best practices for investigation, eradication and recovery to make sure that we don’t restore artefacts from the attack and we’re protected from reoccurrence
– Ben Preston, Field Technical Director, Cohesity
10:50 – 11:20: Driving Diversity in Cybersecurity
This workshop will encourage discussion around gender diversity across the industry, looking at ways we can drive better gender diversity and the benefits of a more diverse workforce:
Topics to be covered will include:
- Current barriers to diversity; where are we and where do we need to be?
- Expanding talent and leadership development opportunities
- Maintaining the internal dialogue: the benefits of collaboration
– Amy Stokes-Waters, Founder and Chief Commercial Officer, Capture the Talent
11:30 – 12:00: Mid-Market Companies shouldn’t compromise on cybersecurity. SaaS Cyber is here to stay
In this roundtable session we will explore how managed service providers can better partner with mid-market organisations to produce shared security outcomes. Discussion points will include:
- Security priorities for mid-market customers
- Desired outputs from MDR providers
- Achieving true security partnership
– Poppaea McDermott – Senior Threat Hunter, Detection & Response Team, WithSecure
11:30 – 12:00: A Six Month Forecast of Data Privacy Challenges
- An insight into the key data privacy challenges and how to prepare
- How can security leaders enforce a comprehensive privacy standard?
- Keeping on top of the changing regulatory landscape
– Cavan Fabris, Lead Partner, Data Privacy & Cybersecurity, Deloitte
Lunch
12:00 – 12:45
Solution Spotlight Sessions
12:45 – 13:30: This focused session is your opportunity to learn more about the cutting–edge technologies transforming the future of the IT Security market. Each solution spotlight lasts just fifteen minutes.
Spotlight Session Four: Closing the Gap on your Cybersecurity and Business resiliency through Managed Services
- With Cybersecurity becoming more and more a focus, as both regulations and security challenges get more scrutiny and complexity to the field, paired with ongoing Digital Transformation journeys, partnering with a managed services provider can help you to quickly close the gaps, identify improvement areas, and getting help to both faster insights and more efficient and focused resource allocation.
- Come to find how Stefanini can help you scale your security program, increase resiliency and partner with your teams to scale up your processes, expertise, and improve your overall business resiliency.
– Nuno Silva, Cybersecurity Portfolio Manager, Stefanini
Spotlight Session Five: A Data Backup Security Perspective: To Help Your CEO Sleep At Night
A CXO typically used to leave the entire aspect of backup and recovery to their IT chiefs. However, after the events of recent years, it is no longer acceptable for an CXO to unquestionably trust their IT Chief that the organization’s data and applications are adequately protected. Instead, more detailed assurances are now required at a higher level.
This presentation helps IT security professionals to be absolutely sure their organization is effectively protected with backup and recovery – from the executive’s perspective.
It also discusses the range of questions and topics a CXO is likely to ask of her/his IT department to ensure that, from the backup and recovery perspective, all reasonable and special
measures are correctly in place to protect their organization. The presentation discusses how to correctly exploit one of the main pillars of security and Business Continuity – advanced backup and recovery software – and what the true value is of that to your organization… including allowing your CEO to sleep at night.
– Rob Morrison. Co-Founder, Bacula Systems
Spotlight Session Six: The Network: Cybersecurity’s Secret Weapon
The network may very well be the most overlooked and underutilised weapon in the defender’s arsenal. It has unique properties that make it essential to cybersecurity, yet many organisations continue to rely on traditional and legacy security tools that provide much less visibility and far fewer accurate threat insights across their cloud, on-premises, and hybrid environments.
In this session we will demonstrate the unique and critical role that the network plays in early detection of advanced threats and in stopping attacks before they do damage.
– Kat Palmer, Regional Sales Manager, ExtraHop
1-2-1 Meetings/Conference Roundtables/Networking
13:40 – 14:50:
13:40 – 14:10: Adapting your Internal Infrastructure in Line with the Evolving Tech Landscape
- From people to process and technology: key infrastructural considerations
- Security by design to meet changing regulatory requirements
- How can we enable architect best practices to mirror security best practices without sacrificing agility?
- When prioritising resources, how can we take a security-minded approach?
– Edward Conway, Director, Security & IT, Mental Health Innovations UK
13:40 – 14:10: Reducing Your SOC TCO With Data Pipelines
Securing your organisation no longer comes down to acquiring the right tools and building the best policies, while managing the flood of noisy, high volume security data and associated costs means the difference between detecting a breach and missing a critical alert. Join Cribl’s round table session to learn how data pipelines put choice and control over data back into the hands of security teams while reducing your SOC TCO.
– James Todd, Technical Director, EMEA, Cribl
14:20 – 14:50: Cyber Recovery – Discussing zero trust and legislation
In this thought leadership session, you will be able to exchange best practices and ideas with your peers relating to ransomware protection and zero trust principles. We will also discuss how legislation is impacting your approach to the information security in your organisation.
- As part of the session, we will address the below questions:
- What impact is DORA and NIS2 having on your InfoSec decisions?
- What security processes and practices have evolved with the increase of ransomware?
- What challenges your organisation has seen in implementing zero trust policy?
– Richard Brackley, Sales Director – Commercial UK&I, Veeam Software
14:20 – 14:50: Data Protection Programmes – Secure Executive Sponsorship
In this roundtable session we will discuss how to secure your key stakeholder buy–in for your data protection and compliance requirements.
How can security support new business initiatives, but ensure that they tick all the data protection and compliance boxes without introducing more risk and crippling themselves with more work? We’ll answer that question during this roundtable session, and provide answers to these other questions:
- What is your greatest data protection concern and business requirement for 2024?
- How to position the value of a strong cybersecurity posture to organisationalstakeholders:
- What are your best practice recommendations for identifying your organisation’s sensitive data?
- How have you balanced the need for security to be an enabler, while reducing the risk of data loss or compliance violations?
- What strategies have proven to be effective at reducing workload on your security and compliance teams from DLP false positives?
– Nick Hogg, Director Technical Training, Fortra
Afternoon Coffee and Networking
14:50 – 15:00
Solution Spotlight Sessions
15:00 – 15:45: This focused session is your opportunity to learn more about the cutting–edge technologies transforming the future of the IT Security market. Each solution spotlight lasts just fifteen minutes.
Spotlight Session Seven: End-to-End Customer Journeys Optimized for Security and Convenience
– Máté Barany, Enterprise Account Executive, Ping
Spotlight Session Eight: Freeing Endpoint Security from Monitor, Detect, Remediate
– Jack Hicks, Senior Presales Engineer, IGEL Technology UK
Spotlight Session Nine: Investigate and Recover from Cyber Attacks Faster with Digital Forensics
When handling incident response, internal/HR-related cases and other enterprise investigations, you need to be able to simplify the process and ensure that you’re able to act in a timely manner. Find out how you can make it easier to collect & analyse data from a range of sources as we explore case studies from different providers and sectors.
– Gavin Hornsey, Solutions Consultant, Magnet Forensics
Closing Keynote Panel
15:45 – 16:15: The Future Role of Technology Leaders: Connecting Business Value to Security.
- The C-level role as a digital business leader: promoting the value proposition of information technology and cyber security
- The increasing importance of diversity in achieving business goals
- How to articulate cyber and information security’s business value to non-technical stakeholders
- Minimizing threats and vulnerabilities AND driving business enablement at an acceptable and cost-effective level of risk
- Talking the language of business in communicating risk
Moderator:
Alan Jenkins, Principal Consultant, The Cyber Security Navigator
Panelists:
Cavan Fabris, Lead Partner, Data Privacy & Cybersecurity, Deloitte
Victor Murineanu, IT and Cybersecurity Leader, Chelsea Football Club
Deepan Shah, Network Architect, BT
Ange Johnson de Wet, Head of Engineering, Commercial and Institutional, Chief Digital and Innovation Office, Natwest Bank
Drinks Reception
16:30
YOUR TECHNOLOGY SHOWCASE
Are you looking to showcase what you have on offer? Connect with the leading decision-makers in IT through thought-leadership, brand awareness, & personal 1-on-1 time. Build your trust & demonstrate your value at EPN IT Vision 2022.
Sponsorship packages can be tailored-made to meet your requirements. Contact the sponsorship team to find out how you can utilise your opportunity to meet the CIO community.
- ITSM
- Identity & Access Management
- Communications
- API
- IOT
- Remote IT
- CRM & ERP
- DevOps
- Network Infrastructure
- 3rd Party Risk
- Cloud Management
- Data Management
- AI & Automation
- Mobile & Applications
- Monitoring & Reporting
- Security
TITANIUM
- Exhibition Space in Tier 1 Area
- Product Demo
- Host a Roundtable
- 5 x 121 meetings in the build up and over the course of the day
Co-branding on All Literature - Priority networking
- Bespoke Thought Leadership Dinner the night before
PLATINUM
- Exhibition Space in Tier 1 Area
- Product Demo/ Keynote Speech
- 5 x 121 meetings in the build up and over the course of the day
- Co-branding on All Literature
- Priority networking
- Host a Roundtable
GOLD
- Exhibition Space in Tier 1 Area
- Product Demo
- 5 x 121 Meetings in the build up and over the course of the day
- Co-Branding on All Literature
- Priority Networking
SILVER
- Exhibition space in Tier 2 Area
- 3 x 121 Meetings in the build-up and over the course of the day
- Co-Branding on Some Literature, Networking Sponsorship
BRONZE
- Exhibition space in Tier 3 Area
- Co-Branding on Some Literature
- Networking Sponsorship
ENTRY-LEVEL SPONSORS
- Branded Table in the Coffee Area
- Networking Sponsorship
Take Part in the Conference / Top 3 ways you can gain exposure
1: Meet the decision-makers of corporate technology. Get to know the people who create digital success.
2: Save time & money by touching- base with your existing clients, making new contacts, & showcasing your expertise all in one place.
3: We know the power of face-to-face business networking. You should be part of the conversation.
Thought-Leadership
Position yourself among the leading experts of IT development & application. Let the IT community know that you are integral expert in the conversation.
Brand Visibility
Get your foot in the door as IT leaders seek for new applications & technologies by showing the solution is out there… they just need to know what it is.
Demonstrating Value
Take part in the Product Demonstrations & showcase your capabilities, so that your potential clients can learn that you are right for them
Maintain Relationships
With f2f being too long missed, reconnect with your existing clients & show that you are ready & wanting more.