- Sophisticated Cyber Threats and Attacks: As the cyber threat landscape continues to evolve with increasingly sophisticated and persistent attacks, learn how to defend against advanced threats that can bypass traditional security measures
- Supply Chain and Third-Party Risk: Brainstorm the best ways to assess and manage the security posture of vendors, partners, and suppliers to prevent potential vulnerabilities from compromised systems
- Zero Trust Implementation: How can you rethink traditional security models, establish strict access controls, and ensure seamless user experiences?
- Regulatory and Compliance Complexities: Navigate a web of regulations, from GDPR and CCPA to emerging laws, and ensure their organization’s data handling practices align with these requirements
- Talent Acquisition and Retention: The persistent shortage of skilled IT professionals continues to challenge CIOs in building and maintaining high-performing teams. What do you need to do to attract top-tier talent, upskill existing employees, and foster a culture of continuous learning to navigate talent scarcity?
WELCOME TO CYBERSEC 2025 Where Visionary Cybersecurity Leaders Unite to Fortify Tomorrow's Digital Frontier!
Discover the ultimate gathering ground for trailblazing CISOs and cybersecurity leaders at CyberSec 2025. As the technology ecosystem continues to evolve at an unprecedented pace, and every digital interaction carries unprecedented importance, the role of the CISO has never been more critical.
Join us at CyberSec 2025 and discover the insights, strategies, and connections that will empower you to safeguard the digital landscape of the future.
CyberSec 2025 is not just a conference; it's a nexus of innovation, collaboration, and forward-thinking insight.
Our high-level keynote presentations, interactive panels and round table discussions, led by industry luminaries and visionaries, will delve into the most pressing challenges and emerging trends in the cybersecurity landscape.
From AI-powered threat detection to blockchain-driven data integrity, our agenda is tailored to empower you with the tools and knowledge to stay ahead of the cyber curve.
Engage with a community of like-minded professionals who share your passion for defending against digital threats, and explore innovative solutions that will shape the future of cybersecurity.
Your seat at the CyberSec 2025 table awaits – let's shape the future together!
OUR PARTNERS...
SOME OF OUR ATTENDEES...
SPEAKERS, WORKSHOP & ROUNDTABLE LEADERS
250
Thought Leaders on Site
30 +
Solutions on Show
57%
of IT leaders have been given extra budget to cope with the post-Covid WFH scenario
71%
of IT leaders prefer physical events to virtual events
42%
of IT leaders identify data security as a top priority
TOPICS TO BE COVERED INCLUDE
Who Should Attend?
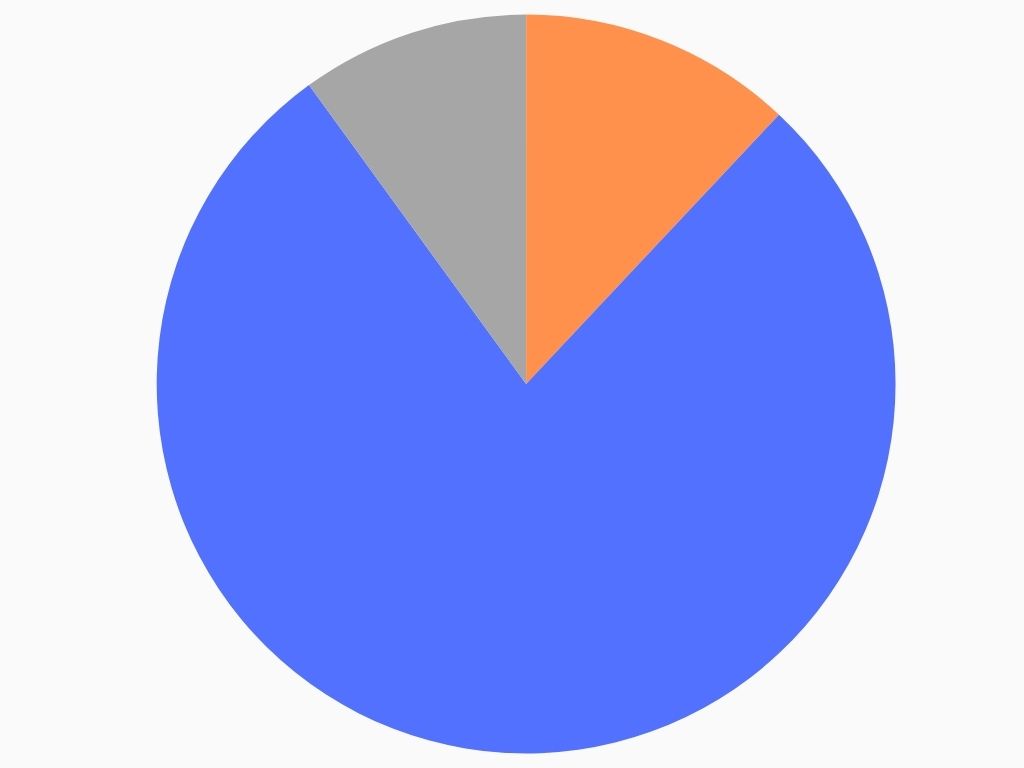
FIELD
IT Security, 78%
Data, 12%
Governance, 10%
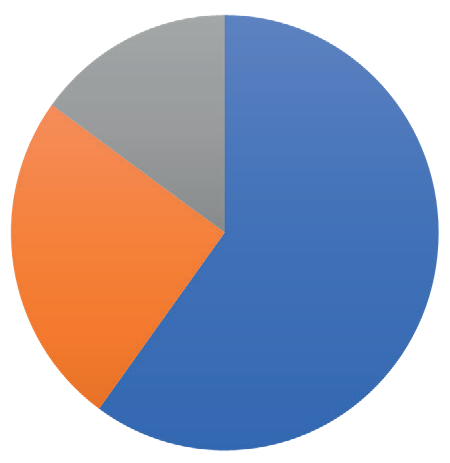
SENIORITY
C-Level, 60%
Directors/VP, 25%
Project Leads, 15%
- WFH & Hybrid
- Digital Transformation
- Cloud
- Collaboration
- Security
- Tooling
- Leadership
“Great discussions with other like-minded experts” – EAO
“A super opportunity to take a step back, reflect, see“A super opportunity to take a step back, reflect, see & learn things from other industries.”& learn things from other industries.” – IQVIA
“The room was truly world class. You could not imagine a better group to discuss what we discussed” – RightCrowd
EPN IT Vision at a Glance / Top 3 reasons you should attend
1: Save time & money by meeting your peers & discovering new technologies all in one place
2: Take part in dynamic discussions, tailored to you and your specific business concerns
3: 10+ hours of networking opportunities. Coordinate meetings, share your experiences, listen to talks.
You have full control of your agenda.
Expert Insights
20 + technology leaders will be delivering data, debate & discussions. Learn from the mistakes & successes of experts from some of the UK’s largest organisations…
Exclusive Features
A new awards show, match-made meetings, a full day of interactive roundtables, complimentary access to co-located events, and much more to take advantage of…
Like-minded Senior Peers
Meet with CIOs, CISO, CDOs, & CTOs to share experiences & get tangible take-home lessons, in both formal & informal networking opportunities…
New Technologies
Join the expo to see the latest technologies that can transform your business. Product demos available to discover what can work for you…
YOUR AGENDA FOR THE DAY (CLICK BELOW TO EXPAND)
08.00 Registration and Coffee
09.15 Opening Keynote Panel Discussion: Beyond Transformation: Building the Secure, Adaptive Enterprise of the Future”
In an era defined by accelerated disruption — from AI and automation to evolving cyber threats and regulatory demands — CIOs and CISOs are no longer supporting roles; they are co-strategists shaping the enterprise of tomorrow. This panel convenes senior technology and security leaders to explore how organisations can architect secure, adaptive digital ecosystems that drive resilience, innovation, and long-term growth across industries.
- How CIOs and CISOs are enabling new business models and operational agility through secure, scalable platforms
- Elevating the CIO–CISO partnership to board-level strategy — ensuring that innovation and protection go hand-in-hand
- Embedding cybersecurity, data integrity, and privacy as pillars of digital trust and competitive differentiation
- Managing risk and governance across rapidly evolving technology landscapes and extended value chains
- Building adaptable digital foundations that can respond to uncertainty — geopolitical, environmental, regulatory, and technological
Bernd Wenninger, Chief Information Officer, A3M Global Monitoring
Titus Hientzsch, Group Chief Technology Officer, World Freight Company International
Riccardo Riccobene, Senior Information Security Officer, State Street Bank International
Moderated by:
Robert Hellwig, Chief Information Security Officer, University of Siegen
10.00 Solution Spotlight Sessions
Spotlight #1 – Rethinking Ethical Hacking with the Cyber Resilience Platform by Marco Bertozzi, Cyber Risk Consultant, Bug Bounty Switzerland
Spotlight #2 – With Great Power Cloud Comes Great Responsibility – A Live Hacking Experience with the Shared Responsibilities Model in Action by Moritz Gruber, Team Lead and Product Owner of Cloud Pentesting , ATOS International
10.30 Morning coffee
11.00 CYBERSEC Roundtable CYBER1: AI's Hidden Risks: Why Your Current Approach Isn't Enough
The race to deploy generative AI is creating a critical security gap. While leaders recognize the risk, our research shows a staggering 32% of findings in LLM pentests are serious or critical, yet only 21% are ever fixed. This roundtable will address why traditional security practices are insufficient for AI’s unique attack surface. We will focus on pragmatic strategies to close the dangerous remediation gap between the rapid pace of innovation and the reality of your security posture.
- The True AI Attack Surface: Discover why traditional vulnerabilities like injections remain the top threat and how they are exploited in new ways that automated scanners miss
- Why Human-Led Testing is Crucial: Understand how creative, human-led pentesting uncovers the business logic flaws in AI systems that automated tools are blind to
- Closing the Remediation Gap: Learn actionable strategies to overcome the “people, process, and technology” challenges that lead to a low fix rate for critical AI vulnerabilities
- Building a Defensible AI Security Program: Move beyond checklists to integrate specialized offensive security into your AI lifecycle, ensuring you can manage risk effectively
Christopher Elisan, Head of Offensive Security Research and Community, Cobalt
11.00 CYBERSEC Roundtable CYBER2: Cybersecurity Landscape: Shifting from Prevention to Resilience and Containment
The cybersecurity landscape has fundamentally shifted from a prevention-focused mindset to one of cyber resilience and breach containment.
- How accepting breach inevitability changes your security architecture
- Building containment strategies that limit lateral movement from day one
- Managing executive expectations during Zero Trust transformation
- Quantifying the business impact of breach containment
- How AI is becoming central to Zero Trust architectures, enabling more nuanced risk assessments and dynamic policy enforcement
Alex Goller, Principal Sales Engineer, Illumio
12.00 CYBERSEC Roundtable CYBER3 Layers of Trust: Modern Security from Defence in Depth to AI Risk with HackerOne
Join HackerOne for an exclusive roundtable session exploring how today’s leading security teams are evolving their Defence in Depth strategies to meet tomorrow’s threats. We’ll break down what modern, multi-layered security really looks like — from vulnerability disclosure to continuous pentesting — and dive into one of the most urgent challenges facing security leaders today: securing AI systems.
In the second half of the session, we’ll explore how AI red teaming is reshaping how organisations identify and mitigate risks in AI models, aligning with responsible innovation and regulatory expectations.
This interactive session is designed for security leaders, and innovators looking to stay ahead of attackers, secure emerging technologies, and build resilient, trustworthy systems.
Uwe Schäfer, Senior Manager, HackerOne
Raffaele Clementelli – Senior Account Executive, HackerOne
12.00 CYBERSEC Roundtable CYBER4: Securing the Software Supply Chain — Governance, Assurance, and Resilience
- Building a unified vendor risk framework spanning procurement, legal, product, and security
- Tiering suppliers by business criticality and setting control baselines for each tier
- Requiring and verifying SBOMs, coordinated vulnerability disclosure, and secure update practices
- Enabling continuous monitoring for third-party exposure and compromise indicators
- Contracting for incident notification SLAs, right to audit, and data residency commitments
- Designing contingency playbooks for vendor outages, takedowns, and extortion scenarios
- Reporting board-level metrics on third-party risk reduction and supply chain resilience
Nauman Saleem, Senior Security Engineer, Hyundai AutoEver Europe
12.45 Lunch and Networking
13.30 CYBERSEC KEYNOTE: AI-Powered Web Defense: Stopping Over 2M Attacks, Exposing 20 Lethal Web Patterns & 2,000 Malware IPs
Facing one million daily web requests hitting our WAF—not all benign—our AI-powered regex suite separates friend from foe, ensuring only legitimate traffic reaches our 150+ live web applications. We’ve processed over 300 million requests and counting, blocking over 2 million attack payloads without disrupting business. Using ChatGPT, Grok, Gemini, and Claude, we crafted regex patterns that exposed 20 lethal web attack vectors tied to malware, coin miners, and trojans. Ongoing tuning slashed false positives from 0.9% to 0.1%, with further gains ahead. Reporting 2,000 malware-serving IPs to URLHaus triggered over 550+ takedowns. This talk shares our dynamic methodology, statistics, and insights, empowering attendees to strengthen defenses affordably. Join us to discover how AI is revolutionizing web security today—and setting the foundation for even stronger protection tomorrow.
Ashar Javed, Chief Information Security Officer, Hyundai AutoEver Europe GmbH
14.30 Keynote Presentation: Raise the Bar - Three Levers to Control your Future Business Model and your Career
With technology being the no.1 value creator of our times and unprecedented capabilities of AI available it’s up to CIOs to prepare their organizations best for the productivity wave
Dr Florian Leser, Head of Data Analytics & AI, KKH
15.00 End of Conference
YOUR TECHNOLOGY SHOWCASE
Are you looking to showcase what you have on offer? Connect with the leading decision-makers in IT through thought-leadership, brand awareness, & personal 1-on-1 time. Build your trust & demonstrate your value at EPN IT Vision 2025.
Sponsorship packages can be tailored-made to meet your requirements. Contact the sponsorship team to find out how you can utilise your opportunity to meet the CIO community.
- ITSM
- Identity & Access Management
- Communications
- API
- IOT
- Remote IT
- CRM & ERP
- DevOps
- Network Infrastructure
- 3rd Party Risk
- Cloud Management
- Data Management
- AI & Automation
- Mobile & Applications
- Monitoring & Reporting
- Security
TITANIUM
- Exhibition Space in Tier 1 Area
- Product Demo
- Host a Roundtable
- 5 x 121 meetings in the build up and over the course of the day
Co-branding on All Literature - Priority networking
- Bespoke Thought Leadership Dinner the night before
PLATINUM
- Exhibition Space in Tier 1 Area
- Product Demo/ Keynote Speech
- 5 x 121 meetings in the build up and over the course of the day
- Co-branding on All Literature
- Priority networking
- Host a Roundtable
GOLD
- Exhibition Space in Tier 1 Area
- Product Demo
- 5 x 121 Meetings in the build up and over the course of the day
- Co-Branding on All Literature
- Priority Networking
SILVER
- Exhibition space in Tier 2 Area
- 3 x 121 Meetings in the build-up and over the course of the day
- Co-Branding on Some Literature, Networking Sponsorship
BRONZE
- Exhibition space in Tier 3 Area
- Co-Branding on Some Literature
- Networking Sponsorship
ENTRY-LEVEL SPONSORS
- Branded Table in the Coffee Area
- Networking Sponsorship
Take Part in the Conference / Top 3 ways you can gain exposure
1: Meet the decision-makers of corporate technology. Get to know the people who create digital success.
2: Save time & money by touching- base with your existing clients, making new contacts, & showcasing your expertise all in one place.
3: We know the power of face-to-face business networking. You should be part of the conversation.
Thought-Leadership
Position yourself among the leading experts of IT development & application. Let the IT community know that you are integral expert in the conversation.
Brand Visibility
Get your foot in the door as IT leaders seek for new applications & technologies by showing the solution is out there… they just need to know what it is.
Demonstrating Value
Take part in the Product Demonstrations & showcase your capabilities, so that your potential clients can learn that you are right for them