- Sophisticated Cyber Threats and Attacks: As the cyber threat landscape continues to evolve with increasingly sophisticated and persistent attacks, learn how to defend against advanced threats that can bypass traditional security measures
- Supply Chain and Third-Party Risk: Brainstorm the best ways to assess and manage the security posture of vendors, partners, and suppliers to prevent potential vulnerabilities from compromised systems
- Zero Trust Implementation: How can you rethink traditional security models, establish strict access controls, and ensure seamless user experiences?
- Regulatory and Compliance Complexities: Navigate a web of regulations, from GDPR and CCPA to emerging laws, and ensure their organization’s data handling practices align with these requirements
- Talent Acquisition and Retention: The persistent shortage of skilled IT professionals continues to challenge CIOs in building and maintaining high-performing teams. What do you need to do to attract top-tier talent, upskill existing employees, and foster a culture of continuous learning to navigate talent scarcity?
WELCOME TO CYBERSEC 2025 Where Visionary Cybersecurity Leaders Unite to Fortify Tomorrow's Digital Frontier!
Discover the ultimate gathering ground for trailblazing CISOs and cybersecurity leaders at CyberSec 2025. As the technology ecosystem continues to evolve at an unprecedented pace, and every digital interaction carries unprecedented importance, the role of the CISO has never been more critical.
Join us at CyberSec 2025 and discover the insights, strategies, and connections that will empower you to safeguard the digital landscape of the future.
CyberSec 2025 is not just a conference; it's a nexus of innovation, collaboration, and forward-thinking insight.
Our high-level keynote presentations, interactive panels and round table discussions, led by industry luminaries and visionaries, will delve into the most pressing challenges and emerging trends in the cybersecurity landscape.
From AI-powered threat detection to blockchain-driven data integrity, our agenda is tailored to empower you with the tools and knowledge to stay ahead of the cyber curve.
Engage with a community of like-minded professionals who share your passion for defending against digital threats, and explore innovative solutions that will shape the future of cybersecurity.
Your seat at the CyberSec 2025 table awaits – let's shape the future together!
OUR CONFIRMED PARTNERS...
SOME OF OUR ATTENDEES...
SPEAKERS, WORKSHOP & ROUNDTABLE LEADERS
250
Thought Leaders on Site
30 +
Solutions on Show
57%
of IT leaders have been given extra budget to cope with the post-Covid WFH scenario
71%
of IT leaders prefer physical events to virtual events
42%
of IT leaders identify data security as a top priority
TOPICS TO BE COVERED INCLUDE
Who Should Attend?
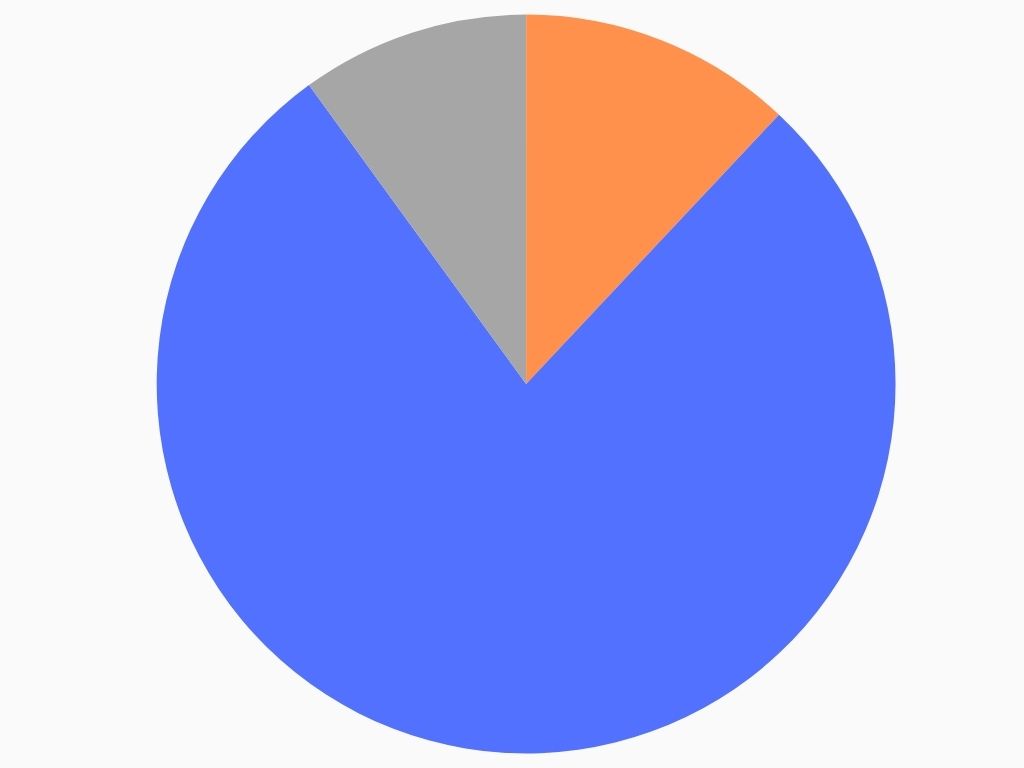
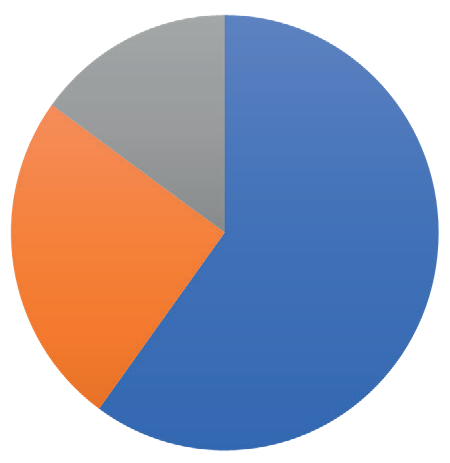
FIELD
IT Security, 78%
Data, 12%
Governance, 10%
SENIORITY
C-Level, 60%
Directors/VP, 25%
Project Leads, 15%
- WFH & Hybrid
- Digital Transformation
- Cloud
- Collaboration
- Security
- Tooling
- Leadership
“Great discussions with other like-minded experts” – EAO
“A super opportunity to take a step back, reflect, see“A super opportunity to take a step back, reflect, see & learn things from other industries.”& learn things from other industries.” – IQVIA
“The room was truly world class. You could not imagine a better group to discuss what we discussed” – RightCrowd
EPN IT Vision at a Glance / Top 3 reasons you should attend
1: Save time & money by meeting your peers & discovering new technologies all in one place
2: Take part in dynamic discussions, tailored to you and your specific business concerns
3: 10+ hours of networking opportunities. Coordinate meetings, share your experiences, listen to talks.
You have full control of your agenda.
Expert Insights
20 + technology leaders will be delivering data, debate & discussions. Learn from the mistakes & successes of experts from some of the UK’s largest organisations…
Exclusive Features
A new awards show, match-made meetings, a full day of interactive roundtables, complimentary access to co-located events, and much more to take advantage of…
Like-minded Senior Peers
Meet with CIOs, CISO, CDOs, & CTOs to share experiences & get tangible take-home lessons, in both formal & informal networking opportunities…
New Technologies
Join the expo to see the latest technologies that can transform your business. Product demos available to discover what can work for you…
YOUR AGENDA FOR THE DAY (CLICK BELOW TO EXPAND)
08:00 Registration and Coffee
09:00 Opening Keynote Panel Discussion: Beyond 2025: The Future of IT and Cybersecurity in the Age of AI
- Predictions for the evolution of IT and cybersecurity roles as AI evolves
- Emerging technologies: how will advancements redefine opportunities and threats?
- Exploring how cross-functional teams and strategic partnerships can drive value
- Legacy vs. innovation: strategies for modernizing legacy systems while embracing disruptive technologies
Rafal Pluta, Global Head – CyberSecurity, Liebherr Group
Adrian Pojar, Director Information Security, Allianz Technology
Florian Nyffenegger, Lead Digital Transformation & AI, IGS GmBH
Sharan Kaur, VP, Swiss InsureTech Hub
Moderated by:
Andra-Irina Vasile, Senior CyberSecurity Strategist, SIX
09:30 Solution Spotlight Sessions
Solution spotlight #1 – Predictive Security Testing for Enterprises. Self-Learning, Plug-and-Play, Data-Driven – Sandro Nafzger, CEO & Co-Founder, Bug Bounty
Solution spotlight #2 – A Day in the Life of a File by Kolja Oswald, Regional Sales Manager, OPSWAT
Solution spotlight #3 – Prevention before Detection – Staying One Step Ahead of Attackers with XM Cyber by Tilman Epha, Sales Director DACH, XM Cyber
10:15 Morning Coffee and Networking
10:40 CYBERSEC Roundtable CYBER1: Illuminating the Blind Spot: IoT & OT Security at the Core of Resilience
As critical infrastructure grows increasingly connected, security leaders face escalating cyber-physical risks — and IoT often remains a security blind spot. This roundtable brings together CISOs and senior executives to explore strategic governance, practical resilience building, and clear accountability for IoT security.
Join your peers to discuss how to:
- Uncover and address hidden vulnerabilities across IT, OT, and IoT
- Clarify ownership and budget responsibility for IoT security
- Strengthen operational resilience through testing and incident readiness
- Align security strategy with board-level risk and regulatory priorities
- Build collaboration across industries, regulators, and vendors
Camilla Bassoli, International Account Manager – DACH + EE, Nozomi Networks
11:25 CYBERSEC Roundtable CYBER2: Trust no file: Minimizing file-borne threats in a zero-trust world.
Even in a zero-trust architecture, files often remain the weakest link. At this roundtable we discuss strategies for reducing file-borne risks without sacrificing productivity. Talking points include layered defense models, deep content inspection, and regulatory alignment for critical industries.
Discussion points:
- ”Trust no file, trust no device.’’ and how it applies to various organizations
- Protection from file-borne threats beyond malware scanning
- Compliance: How regulators (DORA, BAIT, FINMA, NIS2) are implicitly pushing for file-level integrity and traceability
Kolja Oswald, Regional Sales Manager, OPSWAT
12:10 CYBERSEC Roundtable CYBER3: Cyber Risk Management Meets Reality – Pathways to Resilience
Only an end-to-end approach enables comprehensive cyber risk management and the development of true resilience.
- Cloud security ensures seamless protection across all systems
- Zero Trust as a dynamic, multi-layered defense strategy
- Threat Intelligence & Defense supports data-driven decision-making
Virginia Lo Re, Head of Strategic Sales DACH, Trend Micro
12:45 Lunch and Networking
13:45 CYBERSEC Roundtable CYBER4: How to Reduce your Downtime from Days to Minutes
- Disaster risk assessment and identification of critical asset
- Business impact of downtime and quantifying data loss
- Disaster Recovery (DR) Planning – best practices
- Assuring easy and meaningful DR testing with compliance documentation
Reinhard Zimmer, Software Specialist, HPE Zerto
14:30 Closing Keynote Panel: Securing the Digital Core: Balancing Innovation, Agility, and Cyber Resilience
Thomas Stadler, CIO, BBC Group and
Simon Dejung, Former Chief Underwriting Officer, Global Cyber and Technology
Lee Mössner, CyberSecurity Officer, UBS
Moderated by:
Adrian Ciortea, Senior CyberSecurity Principal
15:00 End of Conference
YOUR TECHNOLOGY SHOWCASE
Are you looking to showcase what you have on offer? Connect with the leading decision-makers in IT through thought-leadership, brand awareness, & personal 1-on-1 time. Build your trust & demonstrate your value at EPN IT Vision 2025.
Sponsorship packages can be tailored-made to meet your requirements. Contact the sponsorship team to find out how you can utilise your opportunity to meet the CIO community.
- ITSM
- Identity & Access Management
- Communications
- API
- IOT
- Remote IT
- CRM & ERP
- DevOps
- Network Infrastructure
- 3rd Party Risk
- Cloud Management
- Data Management
- AI & Automation
- Mobile & Applications
- Monitoring & Reporting
- Security
TITANIUM
- Exhibition Space in Tier 1 Area
- Product Demo
- Host a Roundtable
- 5 x 121 meetings in the build up and over the course of the day
Co-branding on All Literature - Priority networking
- Bespoke Thought Leadership Dinner the night before
PLATINUM
- Exhibition Space in Tier 1 Area
- Product Demo/ Keynote Speech
- 5 x 121 meetings in the build up and over the course of the day
- Co-branding on All Literature
- Priority networking
- Host a Roundtable
GOLD
- Exhibition Space in Tier 1 Area
- Product Demo
- 5 x 121 Meetings in the build up and over the course of the day
- Co-Branding on All Literature
- Priority Networking
SILVER
- Exhibition space in Tier 2 Area
- 3 x 121 Meetings in the build-up and over the course of the day
- Co-Branding on Some Literature, Networking Sponsorship
BRONZE
- Exhibition space in Tier 3 Area
- Co-Branding on Some Literature
- Networking Sponsorship
ENTRY-LEVEL SPONSORS
- Branded Table in the Coffee Area
- Networking Sponsorship
Take Part in the Conference / Top 3 ways you can gain exposure
1: Meet the decision-makers of corporate technology. Get to know the people who create digital success.
2: Save time & money by touching- base with your existing clients, making new contacts, & showcasing your expertise all in one place.
3: We know the power of face-to-face business networking. You should be part of the conversation.
Thought-Leadership
Position yourself among the leading experts of IT development & application. Let the IT community know that you are integral expert in the conversation.
Brand Visibility
Get your foot in the door as IT leaders seek for new applications & technologies by showing the solution is out there… they just need to know what it is.
Demonstrating Value
Take part in the Product Demonstrations & showcase your capabilities, so that your potential clients can learn that you are right for them