- Sophisticated Cyber Threats and Attacks: As the cyber threat landscape continues to evolve with increasingly sophisticated and persistent attacks, learn how to defend against advanced threats that can bypass traditional security measures
- Supply Chain and Third-Party Risk: Brainstorm the best ways to assess and manage the security posture of vendors, partners, and suppliers to prevent potential vulnerabilities from compromised systems
- Zero Trust Implementation: How can you rethink traditional security models, establish strict access controls, and ensure seamless user experiences?
- Regulatory and Compliance Complexities: Navigate a web of regulations, from GDPR and CCPA to emerging laws, and ensure their organization’s data handling practices align with these requirements
- Talent Acquisition and Retention: The persistent shortage of skilled IT professionals continues to challenge CIOs in building and maintaining high-performing teams. What do you need to do to attract top-tier talent, upskill existing employees, and foster a culture of continuous learning to navigate talent scarcity?
WELCOME TO CYBERSEC 2024 Where Visionary Cybersecurity Leaders Unite to Fortify Tomorrow's Digital Frontier!
Discover the ultimate gathering ground for trailblazing CISOs and cybersecurity leaders at CyberSec 2024. As the technology ecosystem continues to evolve at an unprecedented pace, and every digital interaction carries unprecedented importance, the role of the CISO has never been more critical.
Join us at CyberSec 2024 and discover the insights, strategies, and connections that will empower you to safeguard the digital landscape of the future.
CyberSec 2024 is not just a conference; it's a nexus of innovation, collaboration, and forward-thinking insight.
Our high-level keynote presentations, interactive panels and round table discussions, led by industry luminaries and visionaries, will delve into the most pressing challenges and emerging trends in the cybersecurity landscape.
From AI-powered threat detection to blockchain-driven data integrity, our agenda is tailored to empower you with the tools and knowledge to stay ahead of the cyber curve.
Engage with a community of like-minded professionals who share your passion for defending against digital threats, and explore innovative solutions that will shape the future of cybersecurity.
Your seat at the CyberSec 2024 table awaits – let's shape the future together!

SOME OF OUR ATTENDEES...
JUST SOME OF OUR CONFIRMED PARTNERS...
SPEAKERS, WORKSHOP & ROUNDTABLE LEADERS
250
Thought Leaders on Site
30 +
Solutions on Show
57%
of IT leaders have been given extra budget to cope with the post-Covid WFH scenario
71%
of IT leaders prefer physical events to virtual events
42%
of IT leaders identify data security as a top priority
TOPICS TO BE COVERED INCLUDE
Who Should Attend?
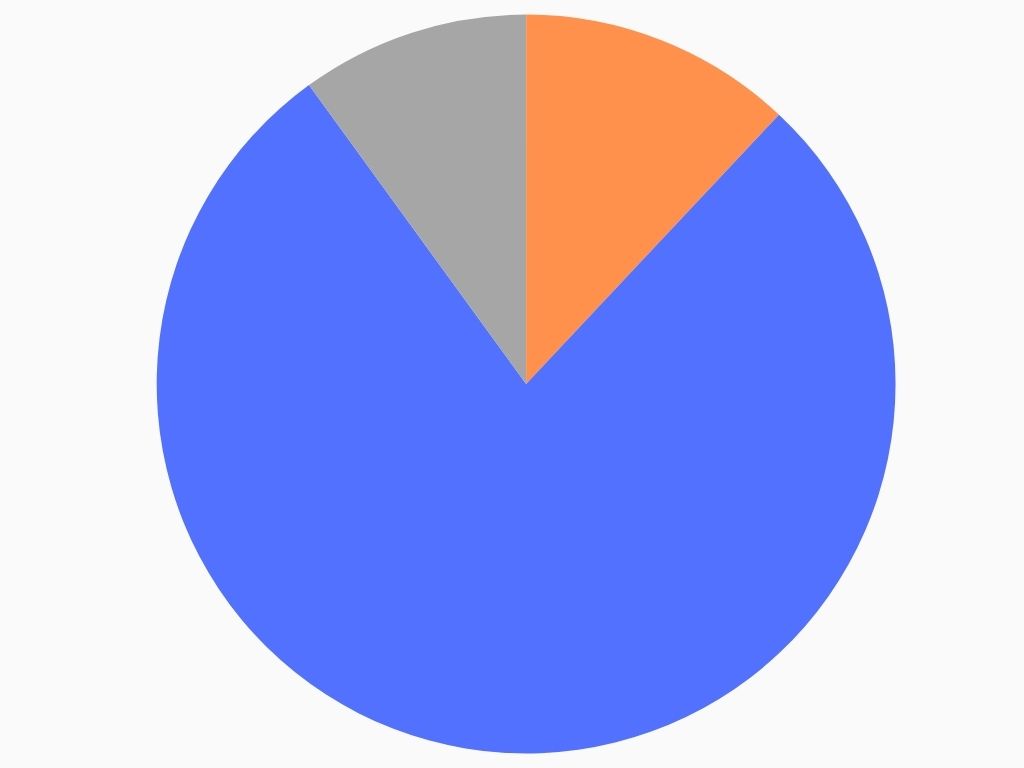
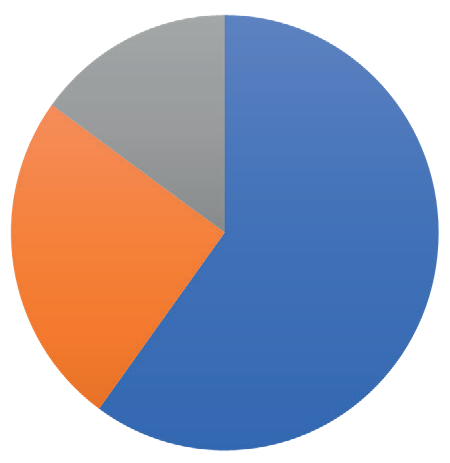
FIELD
IT Security, 78%
Data, 12%
Governance, 10%
SENIORITY
C-Level, 60%
Directors/VP, 25%
Project Leads, 15%
- WFH & Hybrid
- Digital Transformation
- Cloud
- Collaboration
- Security
- Tooling
- Leadership
“Great discussions with other like-minded experts” – EAO
“A super opportunity to take a step back, reflect, see“A super opportunity to take a step back, reflect, see & learn things from other industries.”& learn things from other industries.” – IQVIA
“The room was truly world class. You could not imagine a better group to discuss what we discussed” – RightCrowd
EPN IT Vision at a Glance / Top 3 reasons you should attend
1: Save time & money by meeting your peers & discovering new technologies all in one place
2: Take part in dynamic discussions, tailored to you and your specific business concerns
3: 10+ hours of networking opportunities. Coordinate meetings, share your experiences, listen to talks.
You have full control of your agenda.
Expert Insights
20 + technology leaders will be delivering data, debate & discussions. Learn from the mistakes & successes of experts from some of the UK’s largest organisations…
Exclusive Features
A new awards show, match-made meetings, a full day of interactive roundtables, complimentary access to co-located events, and much more to take advantage of…
Like-minded Senior Peers
Meet with CIOs, CISO, CDOs, & CTOs to share experiences & get tangible take-home lessons, in both formal & informal networking opportunities…
New Technologies
Join the expo to see the latest technologies that can transform your business. Product demos available to discover what can work for you…
YOUR AGENDA FOR THE DAY (Click below to expand)
Registration and Networking
8:15
Opening Keynote
9:00 – 9:30
New EE Does More
- Shaping the business transformation in EE – key challenges and lessons learned
- Winning the household, winning the home screen to win in new markets with platform thinking
- Pioneering a platform approach to drive digital transformation to support the business transformation
- How Data and AI is supporting the company’s approach to modernization
Nathalie Vafiadis, Consumer CIO, BT
Keynote Presentation
9:30 – 10:15
Microsoft Futures: Microsoft’s Strategy, Key Investments and Future Innovation Areas
- An overview of the core incubations and disruptive technologies shaping the cloud’s future and the next wave of innovation across industry, government and society
- Tomorrow’s cloud structure & capabilities: A 3 – 5-year horizon
- How tech will be prepped for changing standards
- How to gain a foothold today in tomorrow’s key technologies
Nick McQuire, Executive Director of Incubation, AI and Quantum, Microsoft
Solution Spotlight
10:15 – 10:30
Solution spotlight-
Guardians of Data: Strategies for robust Data Protection in the Digital Age
Karl Fontanari, Territory Account Manager, Arcserve
Morning coffee
10:30
1-2-1 Meetings/Conference Roundtables/Networking
11:00 – 11:45
How is AI impacting the future of email security?
Despite its growing prominence, misconceptions and myths about AI persist, often clouding its true potential and capabilities. Join this session moderated by Robin Mohan, Libraesva Limited Managing Director, to discuss the realities of AI, dispelling common misconceptions, and exchange views on how AI can be effectively harnessed to enhance email security measures.
Robin Mohan, Managing Director, Libraesva UK
Where’s Wireless?
Join Nick Cox to find out more about the many enterprise applications of 5G Wireless connectivity. In an interactive ‘Where’s Wally?’ inspired workshop participants can win fun prizes, as they discover and discuss the latest applications and use cases for 5G wireless connectivity in organisations like yours.
Nick Cox, Inside Sales Representative – UK&I, Ericsson Enterprise Wireless Solutions
12:00 – 12:45
How Do you Win at Cyber Security, a Strategic Approach
- Review of the technological trends over the last few decades and priorities heading into 2024
- Taking a deeper dive into Visibility and Control – you cannot protect it if you cannot see it
- Maintaining a good IT hygiene posture through Continuous Safeguarding
- Do you have the right tools around Detection and Countermeasure
Rob Broughall, Senior Director – Technical Account Management, Tanium
Secure Predictable Outcomes for a Data-Driven World
Adapting modern practices to deliver radical cyber resilience
Chris Millington, Cyber Resilience & Data Protection Expert, Hitachi Vantara
Disaster Recovery Roundtable TBC
RESERVED for Cobalt
Lunch and Networking
12:45
1-2-1 Meetings/Conference Roundtables/Networking
13:45 – 14:30
Laying the foundations for a secure computing environment
The fast pace of technological change, increasing oversight on data protection and the ever present threat of bad actors are just three reasons why your information security risk profile is fluid.
In this session Steve Macmillan will outline how Protocol Policy Systems (PPS) assists organisations lay the foundations for a secure computing environment so new technologies can be readily adopted, data properly protected and bad actors kept in check.
Steve Macmillan, Managing Director, Protocol Policy Systems
Navigating the New Era of Cyberattack Reporting: Compliance, Communication, and Continuous Assurance
Regulatory pressures are causing CISOs to carefully consider how they communicate security and governance matters, both internally and externally. This interactive discussion aims to shed light on the challenges and opportunities presented by this shifting landscape, emphasising the need for rigorous compliance, transparent communication, and continuous assurance to uphold organisational integrity and resilience.
Understanding the implications of current regulatory rules on cyber incident reporting and disclosure obligations
- Navigating the complexities of compliance beyond certifications, ensuring operational alignment and ongoing adherence to standards
- Implementing robust processes for verifying and validating security claims, such as multi-factor authentication (MFA) implementation and vulnerability remediation
- Enhancing visibility and control over IT environments to mitigate risks associated with siloes, migrations, and changes
- Establishing a culture of continuous assessment and validation to proactively identify and address security gaps and compliance deviations
Phil Cracknell, CISO, UK Defence Contractor
Afternoon Coffee
14:30
Solution Spotlight
14:45 – 15:00
Solution Spotlight –
Applying Multi-Scanning to File Upload Security
Ross Maurer, Solution Engineer, OPSWAT
Keynote Presentation
15:00 – 15:30
Cyber Resilience is About More Than Keeping the Lights On
Alan Jenkins, The Cyber Navigator
Closing Keynote Panel Discussion
15:30 – 16:00
Securing the Future: Collaborative Strategies for Cyber Resilience in the Digital Age
As leaders tasked with safeguarding organisations against ever-evolving cyber threats, it is imperative that CIOs and CISOs unite both expertise and resources to confront these challenges head-on. In this session, our panellists will explore strategic approaches to enhance cyber resilience, foster collaboration between IT and security teams, and fortify defences against cyber adversaries.
- Understanding the evolving cyber threat landscape and the importance of proactive defence strategies
- Building a culture of cyber resilience that prioritizes continuous improvement and adaptation to emerging threats
- Embracing collaboration between CIOs and CISOs to align technology investments with security priorities and business objectives
- Leveraging threat intelligence and information sharing to enhance situational awareness and response capabilities
- Implementing robust incident response and recovery plans to minimize the impact of cyber incidents and ensure business continuity
Phil Cracknell, CISO, UK Defence Contractor
Jon Hurd, VP of InfoSec & Entertainment Technology, Paddle.com
Moderated by: Alan Jenkins, The Cyber Navigator
End of Conference
16:00
YOUR TECHNOLOGY SHOWCASE
Are you looking to showcase what you have on offer? Connect with the leading decision-makers in IT through thought-leadership, brand awareness, & personal 1-on-1 time. Build your trust & demonstrate your value at EPN IT Vision 2024.
Sponsorship packages can be tailored-made to meet your requirements. Contact the sponsorship team to find out how you can utilise your opportunity to meet the CIO community.
- ITSM
- Identity & Access Management
- Communications
- API
- IOT
- Remote IT
- CRM & ERP
- DevOps
- Network Infrastructure
- 3rd Party Risk
- Cloud Management
- Data Management
- AI & Automation
- Mobile & Applications
- Monitoring & Reporting
- Security
TITANIUM
- Exhibition Space in Tier 1 Area
- Product Demo
- Host a Roundtable
- 5 x 121 meetings in the build up and over the course of the day
Co-branding on All Literature - Priority networking
- Bespoke Thought Leadership Dinner the night before
PLATINUM
- Exhibition Space in Tier 1 Area
- Product Demo/ Keynote Speech
- 5 x 121 meetings in the build up and over the course of the day
- Co-branding on All Literature
- Priority networking
- Host a Roundtable
GOLD
- Exhibition Space in Tier 1 Area
- Product Demo
- 5 x 121 Meetings in the build up and over the course of the day
- Co-Branding on All Literature
- Priority Networking
SILVER
- Exhibition space in Tier 2 Area
- 3 x 121 Meetings in the build-up and over the course of the day
- Co-Branding on Some Literature, Networking Sponsorship
BRONZE
- Exhibition space in Tier 3 Area
- Co-Branding on Some Literature
- Networking Sponsorship
ENTRY-LEVEL SPONSORS
- Branded Table in the Coffee Area
- Networking Sponsorship
Take Part in the Conference / Top 3 ways you can gain exposure
1: Meet the decision-makers of corporate technology. Get to know the people who create digital success.
2: Save time & money by touching- base with your existing clients, making new contacts, & showcasing your expertise all in one place.
3: We know the power of face-to-face business networking. You should be part of the conversation.
Thought-Leadership
Position yourself among the leading experts of IT development & application. Let the IT community know that you are integral expert in the conversation.
Brand Visibility
Get your foot in the door as IT leaders seek for new applications & technologies by showing the solution is out there… they just need to know what it is.
Demonstrating Value
Take part in the Product Demonstrations & showcase your capabilities, so that your potential clients can learn that you are right for them